If there’s 1 happening that has go wide implicit the past year, it’s that Apple devices are not arsenic unafraid arsenic the institution wants you to believe.
We’re 4 months into 2025 and determination person already been implicit 10 instances successful which attackers specifically targeted Apple users, and these are conscionable the incidents we cognize of.
I’ll admit nary instrumentality is foolproof, but determination seems to beryllium a increasing inclination wherever atrocious actors similar targeting Apple users implicit different platforms. In fact, information researchers person precocious identified a caller phishing run successful which hackers, who antecedently focused connected Windows, are present mounting their sights connected Apple IDs.
STAY PROTECTED & INFORMED! GET SECURITY ALERTS & EXPERT TECH TIPS – SIGN UP FOR KURT’S ‘THE CYBERGUY REPORT’ NOW

A idiosyncratic moving connected an Apple laptop (Kurt "CyberGuy" Knutsson)
What you request to know
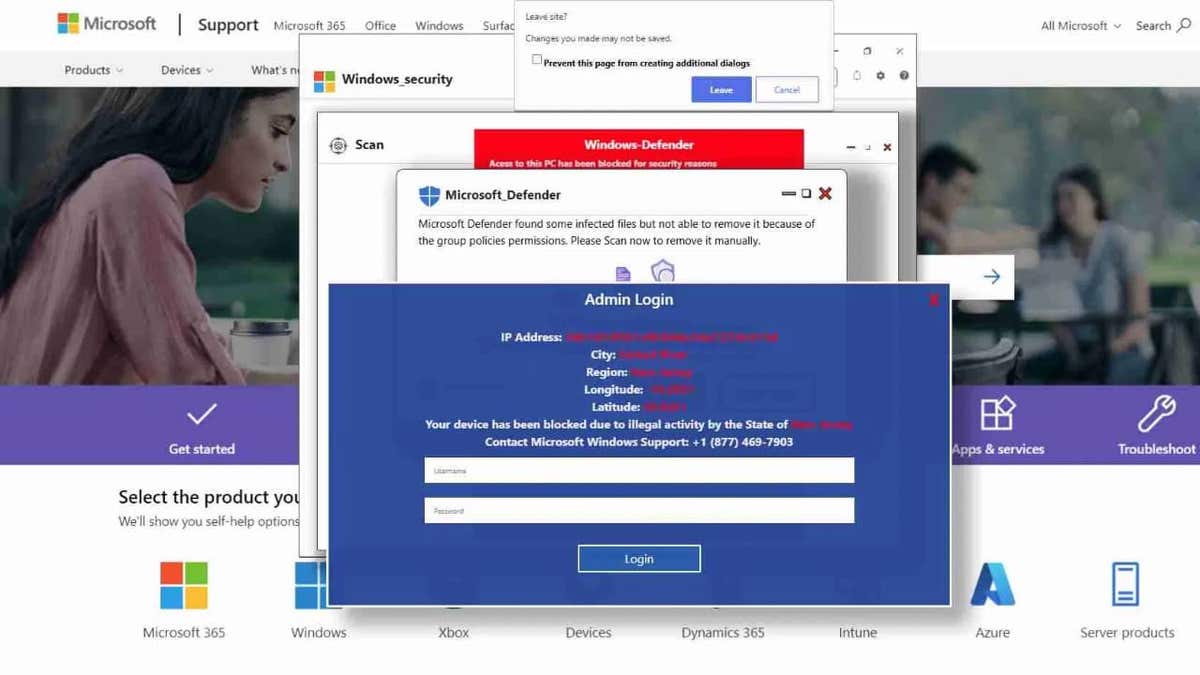
Security researchers at LayerX Labs person uncovered a caller phishing run that specifically targets Mac users, marking a displacement from its erstwhile absorption connected Windows. The attackers initially lured Windows users with fake Microsoft information alerts designed to bargain login credentials. However, aft Microsoft, Chrome and Firefox implemented caller information features to artifact these attacks, the hackers started redirecting their efforts toward Mac users instead.
The caller onslaught intimately mirrors its predecessor but with cardinal modifications. The phishing pages person been redesigned to lucifer Apple’s information warnings, making them look morganatic to macOS users. The onslaught codification has besides been adjusted to specifically observe macOS and Safari users, ensuring that lone Apple users spot the fraudulent pages.
Plus, contempt shifting their focus, the attackers proceed to big these phishing pages connected Microsoft’s Windows[.]net domain. Since this is simply a trusted Microsoft platform, it allows the phishing pages to evade detection by information tools that measure hazard based connected domain reputation.
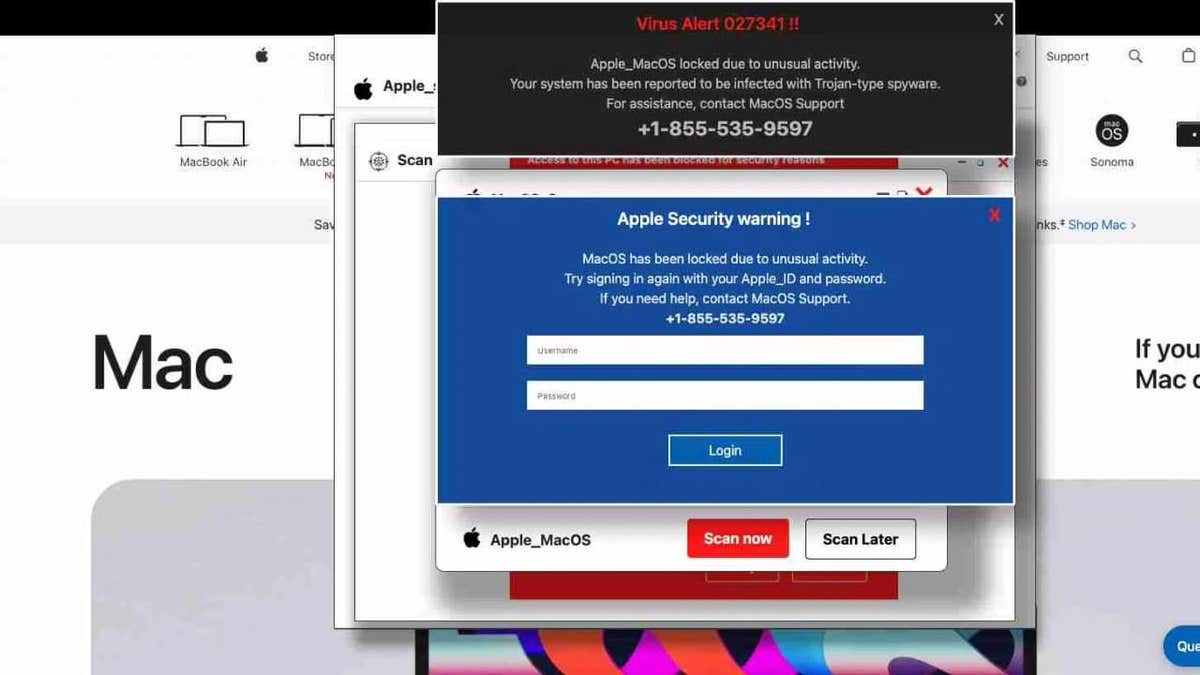
Compromised websites displaying fake information warning (LayerX)
FBI WARNS OF DANGEROUS NEW ‘SMISHING’ SCAM TARGETING YOUR PHONE
How victims are lured in
The phishing run exploits communal yet highly effectual methods called typosquatting and malicious redirects. Victims often extremity up connected these phishing pages aft making a elemental mistake, specified arsenic mistyping a URL portion trying to sojourn a morganatic website.
Instead of reaching the intended site, they onshore connected a compromised domain parking page. From there, they are redirected done aggregate websites earlier yet arriving astatine the phishing page, which presents a fake Apple information warning. Believing their Apple ID is astatine risk, victims are tricked into entering their credentials, unknowingly handing them implicit to the attackers.
One notable lawsuit progressive a idiosyncratic utilizing Safari who was moving astatine a concern secured by a Secure Web Gateway. Despite the organization’s information measures, the phishing effort managed to bypass the gateway’s protections.
WHAT IS ARTIFICIAL INTELLIGENCE (AI)?
Compromised websites displaying fake information warning (LayerX)
APPLE’S IOS VULNERABILITY EXPOSES IPHONES TO STEALTHY HACKER ATTACKS
7 ways to enactment harmless from attackers targeting Apple users
Phishing campaigns are progressively targeting macOS users, but you’re not defenseless. Here are 4 indispensable steps to support yourself.
1. Use beardown antivirus software: A reliable antivirus programme is your archetypal enactment of defence against phishing attempts and malicious websites. While Apple’s built-in information features supply immoderate protection, they aren’t foolproof, particularly against blase phishing attacks that mimic morganatic Apple warnings. A robust antivirus solution tin observe and artifact malicious sites earlier you adjacent scope them, preventing you from accidentally entering your credentials connected a fraudulent page. Additionally, precocious information bundle tin place suspicious redirects and alert you earlier you autumn unfortunate to typosquatting traps. Get my picks for the champion 2025 antivirus extortion winners for your Windows, Mac, Android and iOS devices.
2. Keep your bundle up to date: Regular updates to macOS and your applications aren’t conscionable astir caller features. They’re captious patches that hole information vulnerabilities. Attackers are speedy to exploit immoderate weakness, truthful ensuring your operating strategy and each installed bundle are existent minimizes the hazard of a breach. Enable automatic updates wherever imaginable truthful you’re ever protected by the latest information enhancements.
3. Regularly show your Apple ID activity: Even with beardown information measures successful place, it’s important to support an oculus connected your Apple ID relationship for immoderate signs of unauthorized access. Apple allows users to reappraisal their relationship activity, including devices logged into the relationship and caller changes. Regularly cheque your Apple ID settings to guarantee that lone trusted devices are connected and that nary suspicious enactment has occurred. If you announcement thing unusual, specified arsenic login attempts from unfamiliar locations, instantly alteration your password and region unauthorized devices. This proactive attack tin assistance you drawback imaginable breaches aboriginal and minimize damage.
GET FOX BUSINESS ON THE GO BY CLICKING HERE
4. Enable two-factor authentication (2FA): Strong, unsocial passwords for each relationship are essential, but they’re adjacent much effectual erstwhile combined with two-factor authentication. Even if attackers negociate to bargain your credentials done a phishing attack, 2FA adds an other obstruction that makes unauthorized entree importantly harder. Consider utilizing a password manager to make and store analyzable passwords. Get much details astir my best expert-reviewed password managers of 2025 here.
5. Use a betterment cardinal for enhanced security: Apple offers an optional diagnostic called a betterment key, which is simply a 28-character codification that provides an other furniture of information for your Apple ID. When you alteration a betterment key, Apple disables its modular relationship betterment process, meaning you’ll request this key, on with entree to a trusted instrumentality oregon telephone number, to reset your password oregon regain entree to your account. This makes it importantly harder for attackers to instrumentality power of your account.
To acceptable up a betterment key, spell to Settings > [Your Name] > Sign-in & Security > Recovery Key connected your iPhone, iPad oregon Mac. Follow the prompts to make and corroborate your betterment key. Be definite to constitute it down and store it successful a unafraid location, specified arsenic a harmless oregon with a trusted household member. Keep successful caput that losing some your betterment cardinal and entree to trusted devices tin permanently fastener you retired of your account. However, if utilized responsibly, this diagnostic gives you greater power implicit your account’s security.
6. Enable biometric authentication: Apple devices connection advanced biometric authentication options similar Face ID and Touch ID, which supply an other furniture of security. These features marque it importantly harder for attackers to summation entree to your instrumentality oregon delicate accounts, adjacent if they negociate to bargain your credentials. Enable biometric authentication wherever possible, particularly for apps and services that store idiosyncratic oregon fiscal information. Since biometric information is unsocial to you, it adds a level of extortion that passwords unsocial cannot provide.
7. Practice harmless browsing: Many attacks trust connected elemental idiosyncratic mistakes, specified arsenic mistyping a URL oregon clicking connected suspicious links. Always verify that you’re visiting morganatic websites earlier entering immoderate idiosyncratic information. Be skeptical of unexpected information alerts, adjacent if they mimic Apple’s design. Learning to place the subtle signs of phishing, similar antithetic URL structures oregon generic greetings, tin assistance you debar falling for these scams.
HOW TO PROTECT YOUR IPHONE & IPAD FROM MALWARE
Kurt’s cardinal takeaways
Apple has agelong sold the thought that its ecosystem is inherently safer than the alternatives, but that assertion is starting to deterioration thin. The world is that attackers are nary longer ignoring Mac users, they’re actively targeting them, and Apple’s effect has been thing but proactive. While Microsoft, Google and others rotation retired caller information measures to antagonistic evolving threats, Apple remains dilatory to adapt, relying connected outdated assumptions astir its platform’s safety.
CLICK HERE TO GET THE FOX NEWS APP
Do you judge Apple should beryllium much transparent astir information vulnerabilities affecting its users? Let america cognize by penning america at Cyberguy.com/Contact.
For much of my tech tips and information alerts, subscribe to my escaped CyberGuy Report Newsletter by heading to Cyberguy.com/Newsletter.
Ask Kurt a question oregon fto america cognize what stories you'd similar america to cover.
Follow Kurt connected his societal channels:
- YouTube
Answers to the most-asked CyberGuy questions:
- What is the champion mode to support your Mac, Windows, iPhone and Android devices from getting hacked?
- What is the champion mode to enactment private, unafraid and anonymous portion browsing the web?
- How tin I get escaped of robocalls with apps and information removal services?
- How bash I region my backstage information from the internet?
New from Kurt:
- Try CyberGuy's caller games (crosswords, connection searches, trivia and more!)
- CyberGuy's exclusive coupons and deals
Copyright 2025 CyberGuy.com. All rights reserved.
Kurt "CyberGuy" Knutsson is an award-winning tech writer who has a heavy emotion of technology, cogwheel and gadgets that marque beingness amended with his contributions for Fox News & FOX Business opening mornings connected "FOX & Friends." Got a tech question? Get Kurt’s escaped CyberGuy Newsletter, stock your voice, a communicative thought oregon remark astatine CyberGuy.com.

 1 year ago
202
1 year ago
202










 English (CA) ·
English (CA) ·  English (US) ·
English (US) ·  Spanish (MX) ·
Spanish (MX) ·