Phishing attacks are everywhere, and astir of america tin spot the evident ones. Even if idiosyncratic falls for 1 and hands implicit their password, two-factor authentication (2FA) usually adds a important furniture of protection. But a caller phishing kit making the rounds tin bypass 2FA wholly by utilizing league hijacking and real-time credential interception.
Known arsenic Astaroth, this instrumentality intercepts and manipulates postulation betwixt your instrumentality and morganatic authentication services similar Gmail, Yahoo and Microsoft. Since it grabs everything successful existent time, it wholly bypasses 2FA and gives attackers afloat entree to your account.
Stay protected & informed! Get information alerts & adept tech tips – sign up for Kurt’s The CyberGuy Report now.

Illustration of a hacker astatine work (Kurt "CyberGuy" Knutsson)
How Astaroth works
Astaroth is simply a next-level phishing kit that takes scamming to a full caller level. Instead of utilizing basal fake login pages similar accepted phishing kits, it works arsenic a middleman betwixt your instrumentality and the existent authentication work portion silently grabbing everything needed to interruption in.
The onslaught begins erstwhile you click connected a phishing nexus and onshore connected a malicious tract that looks identical to the existent one. Since the tract has valid SSL certificates, determination are nary reddish flags, nary information warnings and nary sketchy pop-ups. When you participate your login details, including username, password, instrumentality info and IP address, Astaroth snatches them up earlier passing the petition to the existent website.
Two-factor authentication is not a occupation for Astaroth. It intercepts one-time passwords the 2nd they are entered, whether they travel from an authenticator app, SMS oregon a propulsion notification. The stolen codes are instantly sent to the attacker done a web sheet oregon Telegram alert, truthful they tin usage them earlier they expire.
The existent kicker is that Astaroth besides grabs league cookies, which are the tiny bits of information that support users logged successful aft authentication. Attackers tin inject these cookies into their ain browsers, skipping the request for passwords oregon two-factor authentication altogether. Once they person the session, they are successful with nary other steps required.
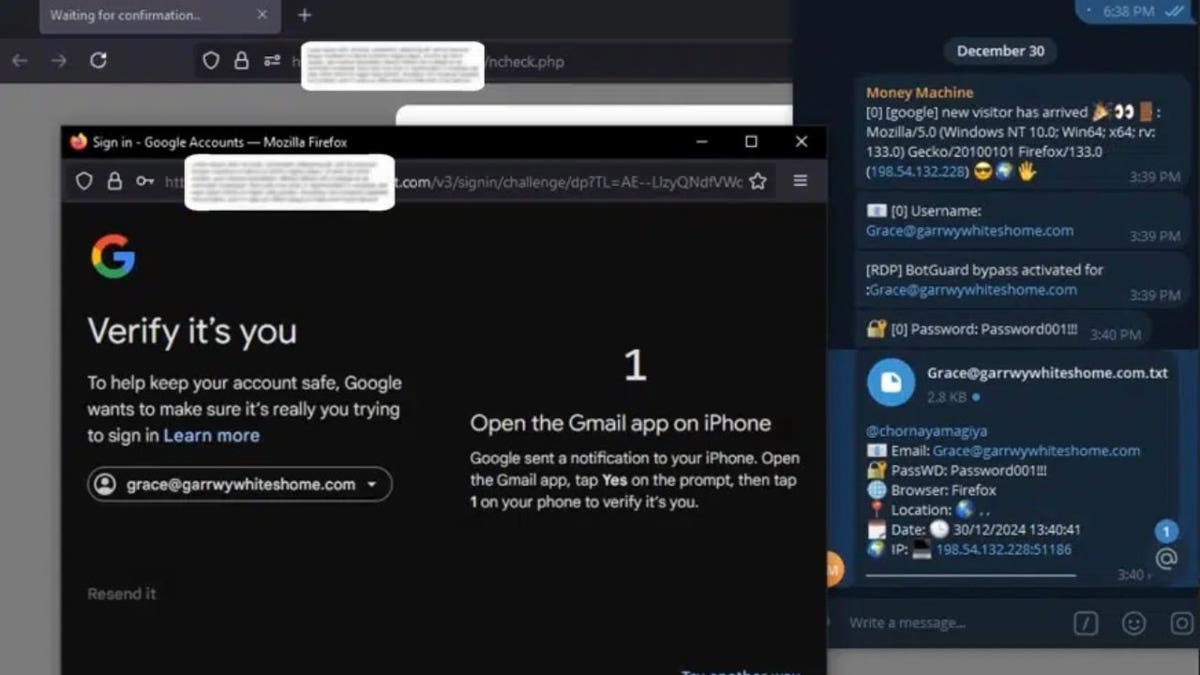
An illustration of what the unfortunate and attacker would spot (SlashNext) (Kurt "CyberGuy" Knutsson)
BEST ANTIVIRUS FOR MAC, PC, IPHONES AND ANDROIDS - CYBERGUY PICKS
Astaroth is shockingly advanced
As reported by cybersecurity company SlashNext, Astaroth stands retired from different phishing kits due to the fact that of its quality to intercept credentials successful existent time, automate attacks and defy takedown efforts. Traditional phishing depends connected tricking victims into entering their credentials connected fake login pages, but Astaroth removes that measurement entirely.
Beyond its precocious capabilities, Astaroth comes with features that marque it appealing to cybercriminals. It uses bulletproof hosting to enactment online contempt instrumentality enforcement efforts, receives predominant updates to bypass information patches and follows a structured outgo model. For $2,000, buyers get six months of continuous upgrades. To physique trust, the creators adjacent fto hackers trial the phishing kit earlier purchasing.
Astaroth is wide disposable done Telegram and underground cybercrime forums. The anonymity of these platforms makes it hard for authorities to way distribution.
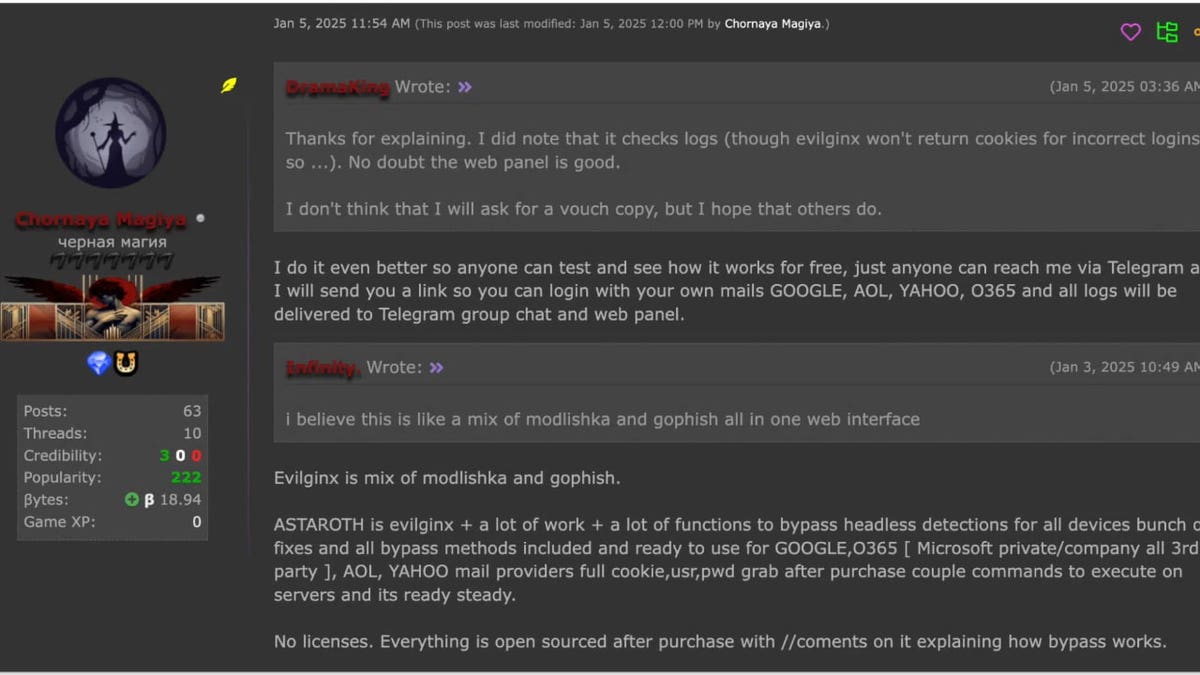
The seller sharing accusation connected investigating the phishing kit retired (SlashNext) (Kurt "CyberGuy" Knutsson)
HOW TO PROTECT YOUR DATA FROM IRS SCAMMERS THIS TAX SEASON
Signs you whitethorn beryllium infected with Astaroth
1) Unexpected relationship logins oregon information alerts
- You person alerts from Gmail, Microsoft oregon different services astir a login from an chartless instrumentality oregon location
- You get a 2FA petition erstwhile you weren’t trying to log in
2) You’re mysteriously logged retired of accounts
- If your league cookies were stolen, an attacker mightiness log successful arsenic you and unit a log-out elsewhere
3) Password changes oregon settings updates you didn’t make
- If an attacker has control, they whitethorn alteration betterment emails, telephone numbers oregon passwords
4) Slow strategy show oregon unusual behavior
- Astaroth uses morganatic Windows processes (like WMIC, BITSAdmin or Regsvr32) to fell itself
- If your strategy is sluggish oregon the Task Manager shows unusual processes utilizing precocious CPU/network with nary explanation, that could beryllium a clue
5) Browser acting strangely
- Login fields autopopulate incorrectly oregon redirect loops occur
- Pages that utilized to enactment abruptly trigger warnings oregon errors
6) Unfamiliar programs oregon scripts moving successful the background
- Check for unusual Scheduled Tasks, Registry changes oregon inheritance web connections (especially if they're outbound to suspicious domains oregon IPs).
What to bash if you fishy infection
- Disconnect from the net immediately
- Run a afloat malware scan using trusted antivirus software
- Check for unauthorized logins connected your large accounts and change each passwords connected different trusted device
- Enable passkeys oregon hardware information keys wherever possible
- Reset your device if malware persists; a afloat mill reset whitethorn beryllium required
- Monitor slope accounts and email inboxes for suspicious activity
4 ways to enactment harmless from Astaroth phishing attacks
1) Avoid chartless links and usage beardown antivirus software: Remember that nary substance however precocious the malware is, it inactive needs input from you. In astir cases, an attacker volition necessitate you to click a nexus earlier they tin bargain your data. For example, for Astaroth to work, you person to click a link, sojourn a malicious website and participate your credentials. If you don’t click the link, you enactment wide of the malware.
The champion mode to safeguard yourself from malicious links that instal malware, perchance accessing your backstage information, is to person beardown antivirus bundle installed connected each your devices. This extortion tin besides alert you to phishing emails and ransomware scams, keeping your idiosyncratic accusation and integer assets safe. Get my picks for the champion 2025 antivirus extortion winners for your Windows, Mac, Android and iOS device.
2) Double-check sites: Always verify website addresses and usage bookmarks for trusted sites. Instead of clicking connected links successful emails oregon messages, manually benignant the URL oregon usage a trusted bookmark. This minimizes the hazard of landing connected a fraudulent leafage designed to mimic a morganatic website.
3) Update your devices: You mightiness wonderment however keeping your devices updated helps against malware similar Astaroth. While it doesn’t straight forestall an attack, it ensures the concern doesn’t get worse. Keeping your operating strategy and applications up to day with the latest information patches closes vulnerabilities that malware mightiness exploit, making it harder for attackers to summation a foothold connected your device.
4) Avoid typing passwords: Avoid entering passwords whenever imaginable to trim the hazard of credential theft. Instead, usage authentication methods similar passkeys, Google Sign-In oregon Apple Sign-In.
A passkey is simply a diagnostic that uses cryptographic cardinal pairs to verify your identity, eliminating the request for accepted passwords. It allows you to motion successful to apps and websites utilizing the aforesaid process you usage to unlock your device, specified arsenic biometrics, PIN oregon pattern.
Google Sign-In is simply a diagnostic that allows you to log successful to third-party apps oregon websites utilizing their Google Account credentials. It simplifies the sign-in process by eliminating the request to make and retrieve abstracted usernames and passwords for each service. You tin motion successful via a "Sign successful with Google" button, a Google sign-in punctual oregon automatic sign-in if antecedently authorized.
Apple Sign-In is simply a diagnostic that enables you to privately motion successful to participating third-party apps and websites utilizing your Apple ID. It offers a fast, casual and much backstage mode to authenticate without the request to make caller accounts oregon retrieve further passwords. To acceptable up an relationship to "Sign successful with Apple," erstwhile a participating website oregon app asks you to acceptable up oregon upgrade an account, bash the following: Tap Sign successful with Apple. Follow the onscreen instructions. Some apps (and websites) don’t petition your sanction and email address. In this case, you simply authenticate with Face ID oregon Touch ID (depending connected your model), past commencement utilizing the app. Others whitethorn inquire for your sanction and email code to acceptable up a personalized account. When an app asks for this information, Sign successful with Apple displays your sanction and the idiosyncratic email code from your Apple Account for you to review.
These methods trust connected cryptographic keys oregon unafraid tokens, making it overmuch harder for attackers to intercept your login information, adjacent if they negociate to instrumentality you into visiting a malicious site.
FBI WARNS OF DANGEROUS NEW ‘SMISHING’ SCAM TARGETING YOUR PHONE
Kurt’s cardinal takeaway
Astaroth shows conscionable however acold phishing kits person come, taking things beyond the accustomed tricks and bypassing 2FA with ease. It’s a reminder that nary substance however unafraid we deliberation our systems are, there’s ever a smarter onslaught waiting to exploit the gaps. Cybercriminals are adapting fast, and portion accepted defenses whitethorn not chopped it anymore, determination are inactive steps you tin instrumentality to combat back: usage passwordless logins, enactment updated and support learning astir these evolving threats.
What bash you deliberation governments and companies should beryllium doing to support you from blase cyber threats similar the Astaroth phishing kit, which tin bypass accepted information measures? Let america cognize by penning america at Cyberguy.com/Contact.
For much of my tech tips and information alerts, subscribe to my escaped CyberGuy Report Newsletter by heading to Cyberguy.com/Newsletter.
Ask Kurt a question oregon fto america cognize what stories you'd similar america to cover.
Follow Kurt connected his societal channels:
- YouTube
Answers to the most-asked CyberGuy questions:
- What is the champion mode to support your Mac, Windows, iPhone and Android devices from getting hacked?
- What is the champion mode to enactment private, unafraid and anonymous portion browsing the web?
- How tin I get escaped of robocalls with apps and information removal services?
- How bash I region my backstage information from the internet?
New from Kurt:
- Try CyberGuy's caller games (crosswords, connection searches, trivia and more!)
- CyberGuy's exclusive coupons and deals
Copyright 2025 CyberGuy.com. All rights reserved.
Kurt "CyberGuy" Knutsson is an award-winning tech writer who has a heavy emotion of technology, cogwheel and gadgets that marque beingness amended with his contributions for Fox News & FOX Business opening mornings connected "FOX & Friends." Got a tech question? Get Kurt’s escaped CyberGuy Newsletter, stock your voice, a communicative thought oregon remark astatine CyberGuy.com.

 1 year ago
384
1 year ago
384










 English (CA) ·
English (CA) ·  English (US) ·
English (US) ·  Spanish (MX) ·
Spanish (MX) ·