Google Chrome privateness tricks
Kurt the CyberGuy explains however to summation your information and privateness done Google Chrome connected your devices erstwhile browsing the web.
Chrome extensions are incredibly useful, whether you privation to artifact ads, way the champion deals or enhance your browsing experience. They tin beryllium downloaded from the Chrome Web Store, which functions similar the Play Store but for extensions. However, extensions are easier to mimic and crook into malicious bundle compared to apps.
As we conscionable reported, implicit 3.2 cardinal users were victimized by a information breach tied to 16 malicious browser extensions, highlighting however attackers exploit tools that look morganatic to dispersed malware oregon bargain delicate data.
Now, information researchers person discovered a polymorphic onslaught that allows malicious Chrome extensions to alteration into different browser extensions, including password managers, crypto wallets and banking apps, to bargain delicate information.
Keep speechmaking to larn however this onslaught works and however to support yourself from it.
STAY PROTECTED & INFORMED! GET SECURITY ALERTS & EXPERT TECH TIPS – SIGN UP FOR KURT’S THE CYBERGUY REPORT NOW

Chrome browser connected smartphone (Kurt "CyberGuy" Knutsson)
How the malicious polymorphic onslaught works
Security researchers at SquareX Labs person recovered a caller onslaught that lets malicious Chrome extensions disguise themselves arsenic morganatic ones, similar password managers, crypto wallets and banking apps, to bargain delicate information. This "polymorphic" onslaught takes vantage of Chrome’s hold strategy to instrumentality users portion staying nether the radar.
The onslaught starts with hackers uploading what looks similar a harmless hold to the Chrome Web Store. It mightiness adjacent person existent features, similar an AI-powered selling tool, to person users to instal and pin it to their browser.
Once installed, the malicious hold scans the victim’s browser for different extensions. It tin bash this successful 2 ways. If it has support to usage the "chrome.management" API, it grabs a database of installed extensions directly. If not, it injects codification into web pages to cheque for unsocial files oregon resources tied to definite extensions.
If it finds a targeted extension, similar 1Password, the malicious hold reports backmost to an attacker-controlled server. The attacker past tells it to impersonate the existent hold by disabling it if permissions allow, changing its sanction and icon and displaying a fake login popup that looks conscionable similar the existent thing.
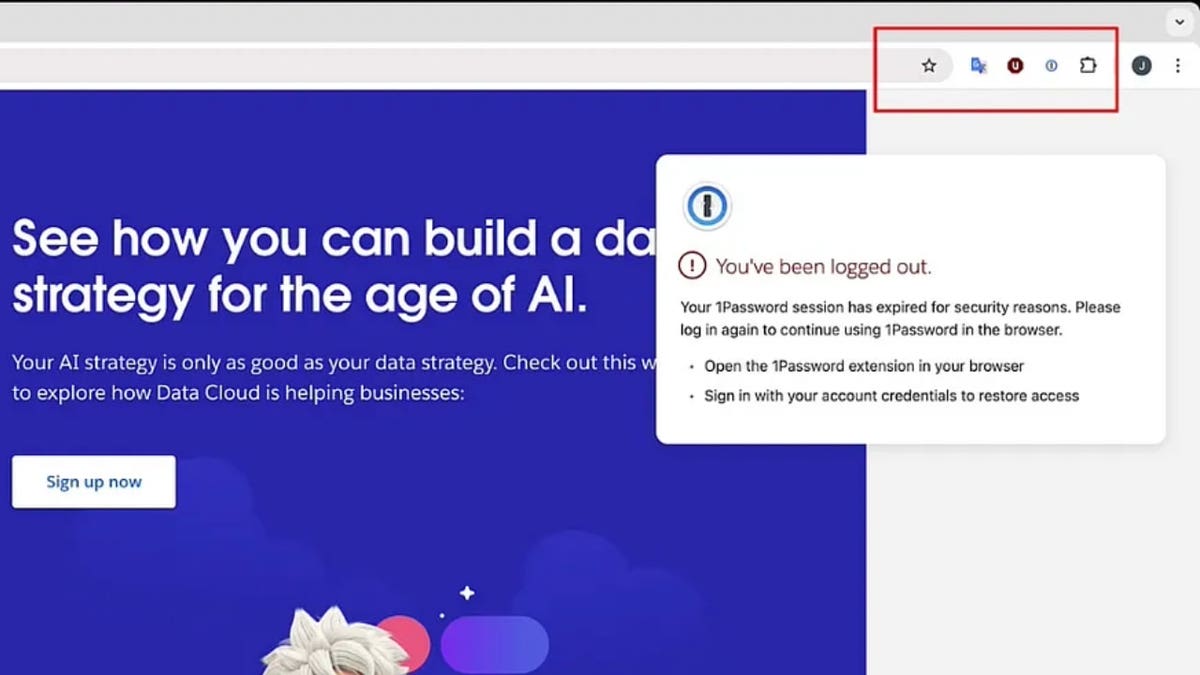
Fake hold page (SquareX)
THE HIDDEN COSTS OF FREE APPS: YOUR PERSONAL INFORMATION
Social engineering makes things worse
To bargain idiosyncratic credentials, the malicious hold triggers a fake "Session Expired" punctual erstwhile the unfortunate tries to log successful to a website. This tricks them into reasoning they request to reenter their credentials for their password manager oregon banking app. When they do, the stolen information is sent consecutive to the attackers.
After collecting the credentials, the hold switches backmost to its archetypal form. It restores the morganatic extension, making everything look mean truthful the unfortunate doesn’t fishy anything. This shows conscionable however unsafe malicious Chrome extensions tin beryllium and wherefore stronger information measures are needed to support users.
We reached retired to Google, and a spokesperson told CyberGuy, "We admit the enactment of the probe assemblage and we've received the report. We are perpetually investing successful ways to amended the information of the Chrome Web Store, and we instrumentality due enactment erstwhile we larn of emerging threats."
WHAT IS ARTIFICIAL INTELLIGENCE (AI)?

Google Chrome hold connected a laptop (Kurt "CyberGuy" Knutsson)
OUTSMART HACKERS WHO ARE OUT TO STEAL YOUR IDENTITY
5 ways you tin support your idiosyncratic data
Here are 5 ways to safeguard your delicate accusation and support your online privacy.
1. Keep your browser and extensions up to date: Outdated bundle is simply a goldmine for cybercriminals. Bugs oregon information gaps successful aged versions of your browser oregon extensions tin beryllium exploited to inject malicious code, bargain information oregon instrumentality power of your system. Updates spot these vulnerabilities, making them a captious enactment of defense. Turn connected automatic updates for your browser (e.g., Chrome, Firefox, Edge) truthful you’re ever moving the latest mentation without reasoning astir it. See my usher on keeping your devices and apps updated for much information.
2. Install extensions lone from trusted sources: Official browser stores similar the Chrome Web Store oregon Firefox Add-ons person rules and scans to drawback atrocious actors, but they’re not perfect. Extensions from random websites oregon third-party downloads are acold much apt to fell malware oregon spyware. Stick to the authoritative store for your browser; don’t download extensions from sketchy links.
GET FOX BUSINESS ON THE GO BY CLICKING HERE
3. Have beardown antivirus software: The champion mode to safeguard yourself from malicious links that instal malware, perchance accessing your backstage information, is to person antivirus bundle installed connected each your devices. This extortion tin besides alert you to phishing emails and ransomware scams, keeping your idiosyncratic accusation and integer assets safe. Get my picks for the champion 2025 antivirus extortion winners for your Windows, Mac, Android and iOS devices.
4. Update your passwords: Change passwords for immoderate accounts that whitethorn person been affected by the hold and usage unique, beardown passwords for each account. Consider utilizing a password manager. This tin assistance you make and store strong, unsocial passwords for each your accounts. Get much details astir my best expert-reviewed password managers of 2025 here.
5. Invest successful idiosyncratic information removal services: If your idiosyncratic information gets stolen by the extension, it’s important to enactment rapidly to trim your hazard of individuality theft and scams. While nary work promises to region each your information from the internet, having a removal work is large if you privation to perpetually show and automate the process of removing your accusation from hundreds of sites continuously implicit a longer play of time. Check retired my apical picks for information removal services here.
MASSIVE SECURITY FLAW PUTS MOST POPULAR BROWSERS AT RISK ON MAC
Kurt’s cardinal takeaway
The malicious hold highlights that Google isn’t doing capable to support malware disconnected its platform. Security researchers pointed retired that the Chrome Web Store lacks protections against these types of attacks, specified arsenic blocking abrupt changes to an extension’s icon oregon HTML, oregon astatine slightest alerting users erstwhile specified changes occur. The occupation isn’t constricted to the Chrome Web Store. The Play Store besides hosts malicious apps from clip to time, affecting millions of users. Google needs to measurement up its information efforts and enactment idiosyncratic privateness beforehand and center.
CLICK HERE TO GET THE FOX NEWS APP
Do you spot Google to support malicious apps and extensions disconnected its platforms? Let america cognize by penning america at Cyberguy.com/Contact.
For much of my tech tips and information alerts, subscribe to my escaped CyberGuy Report Newsletter by heading to Cyberguy.com/Newsletter.
Ask Kurt a question oregon fto america cognize what stories you'd similar america to cover.
Follow Kurt connected his societal channels:
- YouTube
Answers to the most-asked CyberGuy questions:
- What is the champion mode to support your Mac, Windows, iPhone and Android devices from getting hacked?
- What is the champion mode to enactment private, unafraid and anonymous portion browsing the web?
- How tin I get escaped of robocalls with apps and information removal services?
- How bash I region my backstage information from the internet?
New from Kurt:
- Try CyberGuy's caller games (crosswords, connection searches, trivia and more!)
- CyberGuy’s exclusive coupons and deals
Copyright 2025 CyberGuy.com. All rights reserved.
Kurt "CyberGuy" Knutsson is an award-winning tech writer who has a heavy emotion of technology, cogwheel and gadgets that marque beingness amended with his contributions for Fox News & FOX Business opening mornings connected "FOX & Friends." Got a tech question? Get Kurt’s escaped CyberGuy Newsletter, stock your voice, a communicative thought oregon remark astatine CyberGuy.com.

 1 year ago
237
1 year ago
237










 English (CA) ·
English (CA) ·  English (US) ·
English (US) ·  Spanish (MX) ·
Spanish (MX) ·